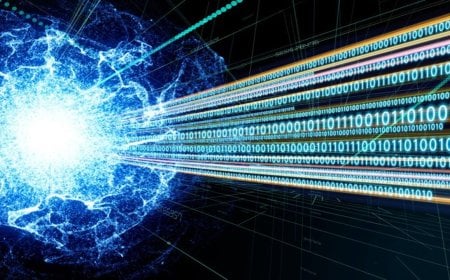
Cyber Alert: 452 Bangladeshi IPs at Risk Due to Outdated IIS Servers

A total of 452 unique IP addresses in Bangladesh are at risk of hacking and cyberattacks, warned BGD e-Gov CIRT, the cyber monitoring and advisory body under the Bangladesh Computer Council (BCC). The risk has emerged due to the use of outdated versions of Microsoft IIS (Internet Information Services) servers in the country’s internet protocol infrastructure.
According to an advisory report published by BGD e-Gov CIRT, “Recent global scanning data shows that over 511,000 internet-facing Microsoft Internet Information Services (IIS) servers running End-of-Life (EOL) versions are exposed worldwide.” It further stated, “Alarmingly, as of yesterday, 452 unique IP addresses in Bangladesh were found running outdated IIS services.”
Based on global scanning insights, it has been noted that these IIS servers will no longer receive security patches or updates from Microsoft. As a result, they are highly vulnerable to data breaches, ransomware infections, service disruptions, and unauthorized access. In response, BGD e-Gov CIRT issued a warning on Tuesday, March 24, urging relevant government and private institutions to urgently prepare a full inventory of their IIS servers, prioritize the isolation of internet-facing servers, and migrate to supported platforms.
Failure to take these measures could disrupt systems across critical sectors, including government services, banking, e-commerce, education, and healthcare. To mitigate risks, organizations have been advised to implement egress filtering at the network level to block unauthorized outbound traffic and to maintain regular vulnerability scanning and patch management.
The advisory also noted that for users of Windows Server 2012/2012 R2, enrolling in Extended Security Updates could serve as a temporary solution. However, older versions such as Windows Server 2008/2003 should be immediately decommissioned or completely isolated from networks. Organizations have been urged to promptly scan their servers to identify vulnerabilities and, if necessary, deploy web application firewalls, enforce strict IP controls, disable unnecessary features, and implement logging and 24/7 monitoring for temporary system hardening.
Additionally, institutions have been called upon to ensure consistent vulnerability scanning and patch management while applying network-level egress filtering. Any suspicious activity or indicators of compromise should be reported immediately to BGD e-Gov CIRT.
DBTech/IH/MUM/OR