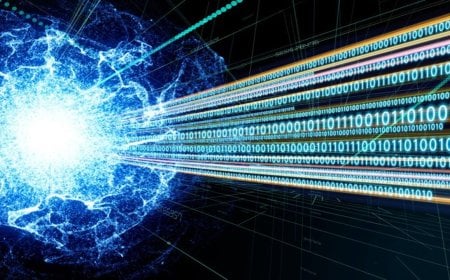
Russian Hackers Exploit Router Vulnerabilities to Steal Passwords and Digital Tokens

The Russian military intelligence agency (GRU) has hacked thousands of office and home Wi-Fi routers worldwide, stealing users’ passwords and digital tokens, U.S. and British security agencies reported on Tuesday, 7 April.
The hacker group known as “Fancy Bear” or “APT28” specifically exploited vulnerabilities in MikroTik and TP-Link routers. They targeted older router models that had not received security updates, gaining control over them. Once compromised, the hackers altered DNS settings to route all internet traffic through their servers, enabling them to capture banking credentials, email passwords, and authentication tokens without users’ knowledge. Even two-factor authentication (2FA) protections were bypassed.
The U.S. Department of Justice and the FBI stated that, in a joint operation, they disabled over 100 servers controlled by the hackers. Settings of affected routers within the United States were also restored to normal.
Paul Chichester, head of the U.K.’s National Cyber Security Centre (NCSC), said the operation demonstrates how router vulnerabilities can be exploited on a massive scale for espionage purposes.
User Recommendations
Security experts have urged all router users to take the following immediate actions:
- Update firmware: Go to the router settings and install the latest firmware. If older models are no longer supported, replace the router.
- Change passwords: Immediately change the router’s default password.
- Factory reset: Perform a factory reset to ensure the router is clean, then reconfigure it.
- Disable remote access: Turn off the remote access option in the router control panel.
DBTech/BMT/OR