Email Earthquake: 183 Million Accounts Exposed in Global Data Leak

In one of the largest email password leaks in recent times, personal information of around 183 million users worldwide has been exposed — a significant portion of them belonging to Google’s Gmail service, according to reports.
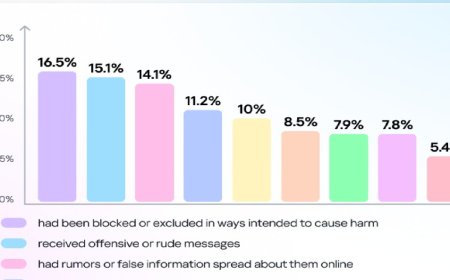
Citing Cyber Insider and Forbes, experts said that although Google’s servers remain secure, there is a growing risk of data reuse and resale. The leaked information has already begun circulating across the dark web. As many users employ the same password across multiple platforms, cybercriminals may gain access to banking, online shopping, or office email accounts, the reports warned.
To prevent panic, cybersecurity experts clarified that Google’s internal systems or servers were not hacked. Instead, the data reportedly originated from malware-infected personal computers and browsers, where attackers had stolen users’ login credentials.
Cybersecurity expert Troy Hunt, who operates the platform “Have I Been Pwned” (HIBP), stated that the newly discovered dataset, titled “Syntient Stealer Log Threat Data,” was not obtained from a single website or company breach. Rather, it was compiled from numerous infected devices worldwide, collecting data from stolen log files.
The leaked data has been added to the HIBP database, enabling users to check whether their personal information has been compromised. By visiting the HIBP website and entering their email address, users can instantly verify if their account details are part of the leaked dataset.
If anyone suspects their Gmail account has been compromised, Google recommends using its “Security Checkup” tool. This feature helps identify suspicious behavior or third-party apps with unusual access to your account. Any “odd or unknown activity” should be removed immediately.
Furthermore, experts strongly advise users to change their passwords without delay if they find their data has been exposed. They recommend using strong, unique passwords that haven’t been used elsewhere and enabling two-factor authentication for added protection.