Identity-Based Cyberattacks Surge Worldwide, Warns Sophos Report

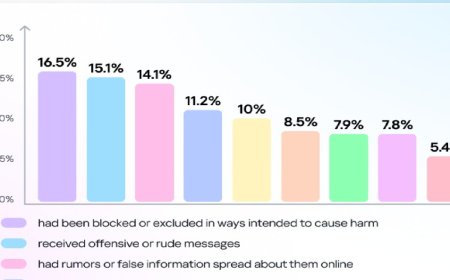
Identity-focused cyberattacks have risen at an alarming rate worldwide. According to statistics from last year, 67 percent of all cyberattacks occurred by exploiting vulnerabilities related to digital identities. Attackers are primarily gaining unauthorized access to organizational networks by using stolen credentials, weak multi-factor authentication (MFA), and insecure identity systems. In particular, hackers are able to infiltrate networks easily in 59 percent of cases where MFA is not used.
Cybersecurity firm Sophos disclosed this information on Monday, March 9, in its Active Adversary Report 2026.
The report notes that although the detection time for cyberattacks—known as dwell time—has dropped to three days, attackers are now spreading through networks extremely quickly and reaching Active Directory within just a few hours. Most attacks, including ransomware incidents and data theft, occur outside regular office hours, when security monitoring tends to be comparatively weaker.
Sophos’ investigation identified 51 ransomware groups, of which 24 are new. Among them, the Akira and Killin groups were found to be the most active. The report also states that although generative AI has not yet been directly used to create major new cyberattack strategies, it is being utilized to enhance the effectiveness of phishing and social engineering campaigns.
To address these growing risks, Sophos has issued several key recommendations. The company emphasized the importance of ensuring proper configuration of MFA to prevent phishing attacks, securing identity frameworks and internet-based services, and promptly patching vulnerabilities in edge devices. It also highlighted the need for organizations to adopt Managed Detection and Response (MDR) or equivalent services to enable continuous 24-hour network monitoring.
DBTech/NHT/EK/OR