Savings Scam Sounds Cybersecurity Siren for Bangladesh’s Financial Sector

The recent savings certificate scam has sounded a strong alarm for Bangladesh’s financial sector. It is not merely a case of cybercrime—it is a stark reflection of structural vulnerabilities within the system itself. A syndicate exploited the National Savings Certificate (NSC) system of the Directorate of National Savings to embezzle around Tk 2.5 million and attempted to withdraw an additional Tk 5 million before the Bangladesh Bank intervened and halted the fraud.
Investigations have revealed disturbing details: the fraudsters changed registered mobile numbers without customer consent, increased transaction limits from Tk 200,000 to Tk 1 million, and even encashed savings certificates before maturity to transfer funds. No one-time passwords (OTPs) were sent to customers during these transactions, indicating insider involvement—making this a textbook case of insider fraud.
The 3P Failure: People, Process, Platform
This fraud reflects a combined failure of the "3P" security model—People, Process, and Platform.
First, password management among officials was weak. Without a strong password policy and mandatory multi-factor authentication (MFA), such intrusions are inevitable.
Second, transactions without OTP verification indicate a procedural failure, not a random error. Such actions cannot occur without internal authorization.
Third, monitoring and auditing mechanisms were ineffective. Sudden changes like mobile number updates, transaction limit increases, or large fund transfers should have triggered automatic anomaly alerts. The absence of any warning proves that monitoring exists on paper but not in practice.
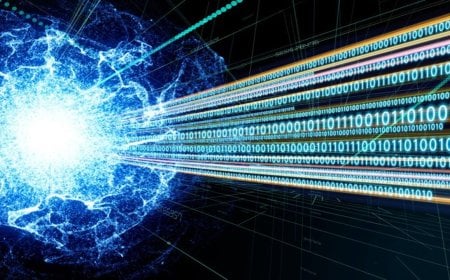
From Trust-Based to Zero Trust
Bangladesh’s financial ecosystem still operates under a “trust-blind” rather than a “trust-based” model—where technology exists, but accountability does not. Security is not solely a matter of software; it demands a blend of policy, training, and responsibility.
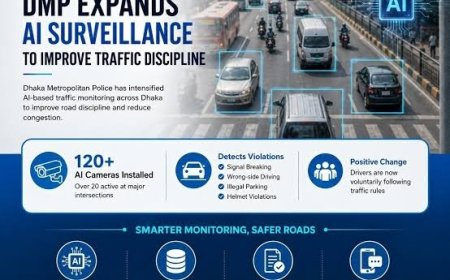
What the sector now needs is a Zero Trust Architecture—a model where no user or device is trusted by default, and every access request is continuously verified.
Way Forward: Synchronizing Technology and Policy
a. Implement Zero Trust: Both public and private financial institutions must be mandated to adopt Zero Trust models.
b. Regular Cyber Audits: At least two independent cybersecurity audits and penetration tests should be conducted annually.
c. IT Governance and Oversight: The “four-eye principle”—requiring approval from two authorized officials for administrative access—should be enforced.
d. Customer Awareness: Customers must understand the risks of sharing OTPs or personal data. Suspicious transactions should be reported immediately.
Law and Enforcement
The swift implementation of the Personal Data Protection Ordinance, 2025, approved in October, is now critical. Once enacted, this law will make data protection and cyber accountability mandatory.
Moreover, an integrated IT governance framework should be formed among Bangladesh Bank, the Directorate of National Savings, and the Ministry of Finance to enable rapid forensic audits and preventive actions.
Conclusion
This incident should not be dismissed as a mere cyberattack—it represents a planned financial crime exploiting technological and institutional weaknesses.
Public funds embody public trust; therefore, the future demands a synchronized security framework across technology, processes, and people.
Bangladesh stands at a pivotal moment in cybersecurity. Unless the nation embraces the principle of “Never Trust, Always Verify,” such frauds will only multiply in the days to come.
Writer: IT Specialist and General Secretary, Bangladesh System Administrators Forum (BdSAF)
Note: The opinions expressed in this commentary are solely those of the author and do not reflect the position of Digital Bangla Media. As a platform that values diverse perspectives, this article is published without editorial alteration. Any disagreement with the views expressed is entirely personal.