How VPNs Work: Understanding Privacy and Protection in the Digital Age

In today’s digital life, personal privacy has become a major concern. Every day, people go online to read news, watch videos, conduct banking transactions, complete office work, or spend time on social media. Behind these routine activities operates an invisible world where personal data constantly travels through networks and servers. One technology that has gained wide attention for helping users remain partially hidden in this environment is the VPN, or Virtual Private Network.
Many users know that a VPN can hide an IP address, allow access to content from other countries, and provide added security on public Wi-Fi networks. However, confusion often surrounds how VPNs actually work. In reality, the concept is not overly complex. With a little attention, it becomes clear what happens behind the scenes.
VPN technology was originally developed for corporate and institutional use, enabling employees working remotely to securely access internal office networks. Over time, it became available to individual users as well. Today, services such as Proton VPN and ExpressVPN offer VPN solutions for personal use.
At its core, a VPN consists of two main components: a server and a client application. The app installed on a computer or smartphone acts as the client, while a powerful remote computer—often located in another country—serves as the VPN server. A secure communication channel is established between the two.
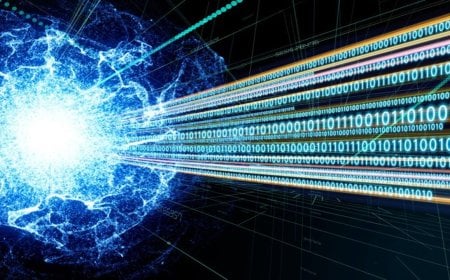
When a VPN is activated, the user’s device first creates a secure connection with the VPN server. From that point onward, all internet activity—browsing websites, streaming videos, or downloading files—is routed through the VPN server before reaching its final destination. Incoming data follows the same route back to the user.
Throughout this process, data remains encrypted, meaning it is locked and unreadable to outsiders. Even if an internet service provider or another third party intercepts the traffic, they can only see that the user is connected to a VPN server—not what data is being exchanged.
This is why VPNs are often described as an online mask. To the outside world, it appears that the VPN server is performing the online activity, not the user. As a result, the user’s real location and IP address remain hidden.
In a standard internet connection, a device sends requests directly through the internet service provider to the destination server, with data traveling in small packets across multiple routes. This system relies on core technologies such as IP and TCP. A VPN intervenes at the beginning and end of this process by encrypting the data before it leaves the device and attaching the VPN server’s address instead.
This method is often referred to as a “tunnel”, creating an invisible passage through which data travels securely between the user and the VPN server. Technically, each data packet is wrapped inside another packet, ensuring that while the destination may be known, the original source remains concealed.
Encryption plays a critical role in this system. Most VPNs use strong encryption standards such as AES-256, the same level of security used by banks and government institutions. Security is typically ensured in two stages: first, the client and server authenticate each other through a verification process, and then high-speed encryption is used for data transmission.
Different VPN protocols, such as OpenVPN, WireGuard, and IKEv2, define how data is encrypted, transmitted, and decrypted. Older, less secure protocols are no longer used by modern VPN services.
The primary reasons for using a VPN are privacy and location flexibility. A VPN makes it harder to directly link browsing activity to an individual user, offering some protection from advertisers and surveillance. It also allows users to access online content from other countries by connecting to foreign servers.
However, experts caution that a VPN is not a magic solution. It cannot hide personal information voluntarily shared on social media, nor does it solve all internet speed issues. Therefore, a VPN should be viewed as one component of digital security, not a complete solution.
In summary, a VPN provides users with an alternative online identity, allowing them to use the internet without revealing their real address. Understanding how this technology works helps users make informed decisions, rather than being misled by exaggerated marketing claims. In an increasingly connected world, such awareness may be the first step toward responsible digital citizenship.
DBTech/BMT/OR