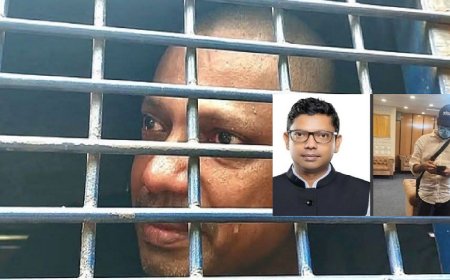
How Digital Evidence Proved the July Uprising War-Crimes Case: Tanvir Hasan Zoha Speaks

Digital evidence played a decisive role in the first verdict of crimes against humanity committed during the July Uprising, which ordered the death penalty for fugitive and deposed Prime Minister and Awami League Chairperson Sheikh Hasina and her Home Minister Asaduzzaman Kamal.
Instructions issued using digital devices to use lethal weapons against protestors, involvement of convicts in the Savar and Jatrabari killings, and especially the video evidence of six bodies being burned in Savar were presented in court as key exhibits.
Although victims did not directly see Sheikh Hasina firing on anyone, investigators proved to the court through digital documents that the shootings occurred on her direct orders. As evidence of these orders, audio recordings of conversations between Sheikh Hasina and former minister Hasanul Haq Inu, former mayor Fazle Noor Taposh, and then Dhaka University Vice-Chancellor Professor Maksud Kamal were submitted to the tribunal.
Additionally, a former army officer had informed the then-Prime Minister via SMS about shots fired from lethal weapons and resulting casualties — this evidence too was submitted.
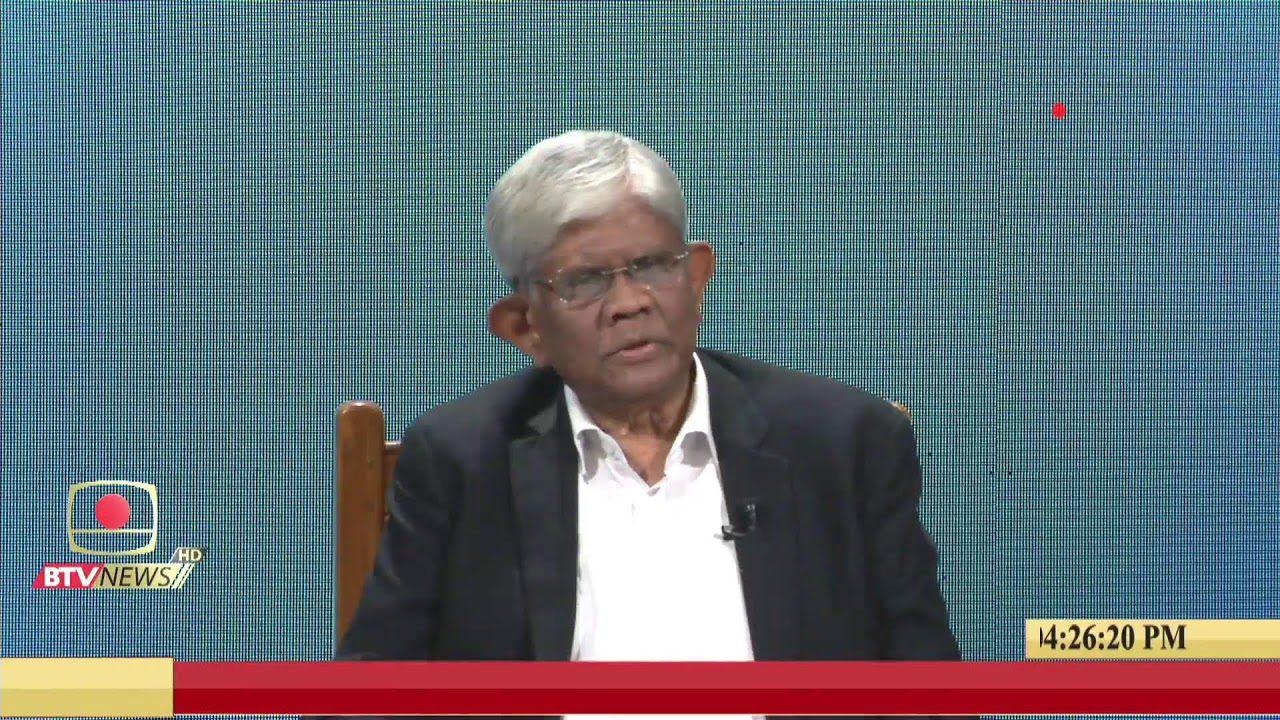
The person who collected and analyzed key digital data and footprints — phone calls, images, videos and more — was Tanvir Hasan Zoha, Prosecutor and Special Investigation Officer of the International Crimes Tribunal. But how did he recover evidence when many perpetrators destroyed data before fleeing? How did he make them admissible in court?
DBTech.news Executive Editor S. M. Imdadul Haq sat with Tanvir Hasan Zoha for detailed answers.
Interview
Q: Since you are busy, let me begin directly — what types and volumes of digital evidence did you seize in the July Uprising war-crimes investigation?
Zoha:
We seized digital evidence across several categories, such as:
-
Mobile phones, laptops, hard disks, pen drives, memory cards
-
CCTV and DVR footage, IP-camera recordings
-
Call Data Records (CDR), SMS/location dumps, BTS/tower data
-
Chats and media content from Facebook, WhatsApp, Telegram, email
-
Video archives from news portals, YouTube, livestreams
-
GPS logs and drone footage where available
In terms of volume, it’s difficult to cite exact numbers, but total data amounted to multiple terabytes. The number of individual items — calls, messages, photos, videos and others — exceeded tens of thousands. Due to safety and court restrictions, I can only give approximate scale, not precise figures.

Q: How and where was forensic analysis conducted?
Zoha:
Forensics were done in several layers:
-
Immediate Seizure & Imaging:
-
At the time of seizure, we used forensic write-blockers to take bit-to-bit images
-
Generated unique MD5/SHA-256 hash values for each device dump
-
-
National Forensic Lab Analysis:
-
At government-approved digital forensic labs (CID, Bangladesh Police)
-
Tools included mobile forensic suites (UFED-type), disk forensic tools, log analyzers, network forensics etc.
-
-
OSINT & Data Correlation:
-
Open-source social media, news articles and archived videos were collected
-
Cross-matched with CDR, location data, and witness testimony
-
Q: People may question whether this evidence was fabricated later. How do you address that?
Zoha:
Digital evidence is used worldwide as valid proof. In this case, all evidence was proven through witnesses as authentic and irrefutable. Investigators eliminated any scope for doubt.
We maintained international standards and used advanced forensic tools. Experts analyzed the data and provided opinions. State witnesses also confirmed the authenticity of most materials.
So, as an investigation officer, I can say the evidence was fully sufficient to prove the crimes.
Q: How many people worked on this?
Zoha:
I won’t give an exact number, but the structure:
-
Digital forensic experts
-
Cyber investigators (investigation officers)
-
Data/timeline analysts
-
OSINT researchers
-
Legal team (prosecutors and researchers)
In major cases, total team size — direct and indirect — often reaches dozens.
Q: Is forensic work still ongoing?
Zoha:
Yes. Even after submitting charges, if new data, devices or cloud information emerge, analysis continues with court approval. Supplementary reports are added when needed.
Q: What challenges did you face recovering evidence from materials destroyed or burned beforehand?
Zoha:
This was the toughest part. Many documents, devices and CCTV systems were deliberately burned or smashed. Chips melted, connectors damaged, boards charred — impossible to read directly. Footage on devices was overwritten.
We used chip-off, JTAG, and advanced recovery methods to salvage partial data.
We reconstructed timelines using tower dumps and CDR.
For destroyed documents, we reconstructed clues from ash, partially burnt paper, photos or video indications.
The biggest challenge was to maintain court-acceptable standards even with fragmented proof. We often had to state clearly:
“This portion is lost, but remaining consistent evidence leads to this inference.”

Q: Many former ruling party leaders claimed the materials were AI-generated. Any truth?
Zoha:
They are genuine. Anyone can verify. International verification mechanisms exist.
BBC and Al Jazeera consulted Ear Shots and Tech Global for forensic checks. They confirmed the call recordings were not AI-generated.
Sheikh Hasina’s son, Sajeeb Wazed Joy, posted on Facebook that the voice was from the 2016 Holey Artisan attack — then deleted it. This deletion itself indicated acknowledgment that the recordings were from the July-August movement.
I believe any international tribunal would reach the same conclusion after cross-checking our evidence.
Q: How did you analyze proof and establish the logic behind the charges?
Zoha:
We focused on:
-
Timeline building
-
Role and command responsibility
-
Consistency testing
Timeline:
We cross-matched dates, locations, towers, phone numbers with photos, videos, livestreams, social media posts, witness statements, medical/post-mortem reports, and confessions.
Role & Command Responsibility:
Identified direct actors, organizers and command-givers from call patterns, meeting records, and chat logs.
Consistency Test:
Checked if witness accounts matched CDR/location/footage.
If at least three out of four sources — victim, eyewitnesses, media reports, digital data — aligned, then it passed.
Our goal was to bring everything to the “beyond reasonable doubt” standard.
Q: With risks of AI manipulation, how did you convince the court to rely on digital evidence?
Zoha:
We demonstrated authenticity through:
-
Hash values
-
Metadata
-
Creation/modification times
-
Device-ID reports
-
Platform-origin logs
-
Manipulation checks
-
Pixel-level and audio spectral analysis
-
Third-party expert opinions when needed
We never used a single clip or image to incriminate anyone.
Digital evidence was always supported by independent proof — eyewitnesses, CDR, physical evidence.
We told the court clearly:
“Digital evidence is not magical — it gains strength through corroboration.”
Q: Was any lethal weapon deployed via drone?
Zoha:
I cannot make case-specific remarks due to sensitivity and sub-judice restrictions.
Generally, establishing drone-based attacks requires:
-
Drone recovery logs
-
Telemetry and video data
-
Eyewitness accounts
-
Physical damage forensics
Social-media rumors or edited videos cannot prove drone weaponization in court.
Q: Did you find evidence that NTMC intercepted and suppressed communications?
Zoha:
To prove such allegations, one needs interception logs, court orders, system-level logs and consistent patterns.
Our principle is simple:
We only comment based on documented, verifiable evidence — not assumptions or political rhetoric.
Q: How much did digital evidence help the first verdict?
Zoha:
In three ways:
-
Clarified the timeline — who was where, when calls were made, when videos were recorded.
-
Broke false alibis — CDR/video disproved claims like “I wasn’t at the scene.”
-
Mapped command chain — not just field operatives but planners and top-level command.
The court valued digital evidence, always alongside other testimonies.
Q: What initiatives did you take to maintain international standards?
Zoha:
We emphasized:
-
Chain of Custody documentation
-
ISO/IEC 27037 & 27041 adherence
-
Capacity building and specialist training
-
Licensed tools plus validated open-source tools
-
Detailed reporting with annexures, logs, screenshots, hash values
-
Transparency and readiness for expert cross-examination
We ensured the tribunal would understand every technical step clearly.
Q: Despite many challenges, you produced decisive digital evidence that shaped the verdict and became part of legal history. How was that possible?
Zoha:
This didn’t happen overnight. From day one, it was clear that without digital evidence, truth could not stand in court.
Three things guided me:
-
Treat data as data — nothing else.
No social pressure, no political narrative.
Every video, audio, location log was verified from its source, metadata and timestamps. -
Base the process on science.
NTMC logs, telecom CDR/IPDR, satellite visuals, device-level traces — everything was placed in one chain.
I never fabricated what didn’t exist and never forced the court to accept what we could not verify. -
Treat the work as national duty, not workload.
Investigating through nights, presenting in court in the morning, and coordinating across agencies in between — I handled all tracks together. The team worked hard, but I had to lead with clear directions.
Ultimately, digital evidence speaks for itself.
It cannot be threatened, distorted, or intimidated.
It always sides with the truth.
I only built the bridge between factual reality and the evidence placed before the court.
If the verdict reflects the strength of these materials, it is because of trust in science, integrity of process, and responsibility to present the truth to the nation.
Q: Thank you for your time despite your busy schedule.
Zoha:
Thank you as well. You asked detailed, thoughtful questions — I hope the answers were equally clear.