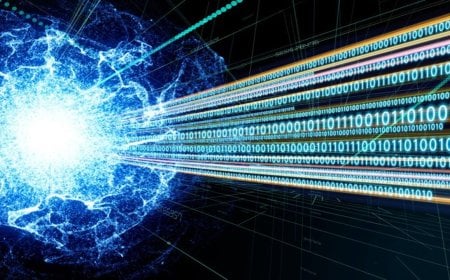
Password Pitfalls Persist: Predictable Patterns Put Accounts at Risk

Weak and easily guessable passwords remain a serious concern in online security, according to cybersecurity firm Kaspersky. A recent study by the company reveals that more than half of leaked passwords end with numbers, making it easier for cybercriminals to hack user accounts.
The findings were published on Sunday, 10 May, based on an analysis of over 231 million unique passwords leaked between 2023 and 2026, conducted in observance of World Password Day. The research report was compiled using data from the company’s Digital Footprint Intelligence service.
The study shows that many users still rely on simple and predictable strategies, such as adding numbers at the beginning or end of passwords. There is also a growing tendency to use popular words, online trends, and emotionally positive terms. Notably, the use of the word “skibidi” has increased 36-fold over the past few years.
Further analysis indicates that among passwords containing only one special character, the most commonly used symbol is ‘@’, followed by ‘.’ and ‘!’. More than half of the passwords end with numbers, while 17 percent begin with numbers. Around 12 percent include birthdates or familiar numerical sequences. Additionally, 3 percent of passwords feature simple keyboard patterns such as “1234.”
Alexey Antonov said, “Many users incorporate familiar numbers, dates, or common symbols, especially at the beginning or end of passwords. This makes them significantly easier to guess through brute-force attacks.”
He added, “Simply adding numbers or special characters to a single word does not make a password secure. Instead, combining several unrelated words along with numbers and special characters is far more effective. Intentional misspellings can also help improve security.”
The research also found that users frequently choose positive words such as ‘love’, ‘magic’, ‘angel’, and ‘eden’, although negative terms like ‘hell’ and ‘devil’ also appear in some cases.
Kaspersky has advised users to adopt long and strong passwords and enable two-factor authentication (2FA). According to the company, passwords created with a mix of random letters, numbers, and special characters are significantly more difficult to crack.
DBTech/RCP/EK/OR