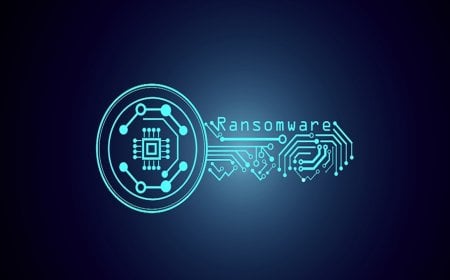
BlueNoroff’s “GhostCall” and “GhostHire” Haunt Global Crypto Firms

Since April 2025, BlueNoroff—a sub-group of the infamous Lazarus Group—has been launching sophisticated cyberattacks on Web3 and cryptocurrency companies across Europe and Asia, including India, Turkey, and Australia. The campaigns, dubbed “GhostCall” and “GhostHire,” employ a seven-stage execution chain featuring four entirely new attack techniques. These include customized crypto stealers, browser and secret stealers, and Telegram credential theft tools to deploy advanced malware.
In the GhostHire campaign, developers are targeted through fake recruiters who invite them to participate in GitHub “challenges” designed to trap them. Meanwhile, GhostCall uses video calls to display phishing links disguised as “updates,” prompting victims to unknowingly install malware. The hackers are reportedly leveraging generative AI to rapidly develop and evolve their malware—introducing new languages, features, and expanding operations globally.
These findings were revealed in a recent report by cybersecurity firm Kaspersky. Detailed information and indicators of compromise related to the GhostCall and GhostHire attacks have been published on Kaspersky’s research platform, Securelist.com.
Researchers advised organizations to carefully verify new contacts or partners, avoid unverified scripts, and use secure communication channels. They also recommended Kaspersky Next for real-time protection, EDR, and XDR capabilities. Additionally, companies were urged to adopt Kaspersky Threat Intelligence Service, Managed Detection and Response (MDR), and Incident Response solutions to strengthen their threat detection and mitigation capacity.
At the Security Analyst Summit held in Thailand, Kaspersky’s Global Research and Analysis Team (GReAT) disclosed the latest activities of the BlueNoroff APT (Advanced Persistent Threat) group. The ongoing GhostCall and GhostHire operations were identified as “highly targeted malicious campaigns” extending the group’s previous SnatchCrypto campaign. These attacks primarily target blockchain developers and corporate executives using macOS and Windows platforms.
The GhostCall campaign utilizes advanced social engineering techniques, with attackers impersonating venture capitalists on Telegram to invite victims to fake online meetings. During these meetings, they encourage targets to install “updates” that are actually malware, granting the attackers remote access to the victims’ systems.
Kaspersky GReAT Security Researcher Sojun Ryu explained, “This campaign involved meticulous deception. The attackers replayed videos from previous victims during arranged meetings to make the calls appear authentic. In doing so, they misled new targets. The harvested information was not only used against direct victims but also leveraged for subsequent supply chain attacks. The attackers exploit trust relationships to gain access to even more corporate and individual systems.”
Senior Security Researcher Omar Amin added, “Since the previous campaign, the attack strategies have evolved beyond stealing cryptocurrency or browser credentials. With generative AI, malware development has become faster and easier, reducing operational complexity. The group is now using AI’s analytical capabilities alongside compromised data to expand its attack surface. We hope our research will help prevent similar harmful campaigns in the future.”