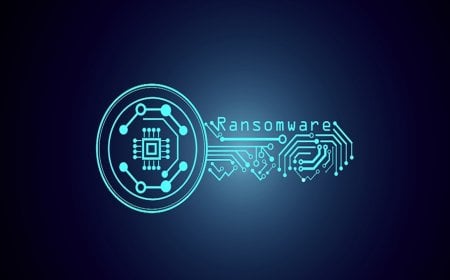
Kaspersky Uncovers Memento Labs’ Espionage Operation Exploiting Chrome Zero-Day
Kaspersky’s Global Research and Analysis Team (GReAT) has found evidence linking “Memento Labs” to a new form of cyber-espionage attack. The findings emerged during an investigation into an Advanced Persistent Threat (APT) campaign named “Operation ForumTroll,” which exploited a zero-day vulnerability in Google Chrome, according to a statement released by Kaspersky on Wednesday, October 29.
The research results were presented at the Security Analyst Summit 2025 held in Thailand. Memento Labs was previously known as “HackingTeam.”
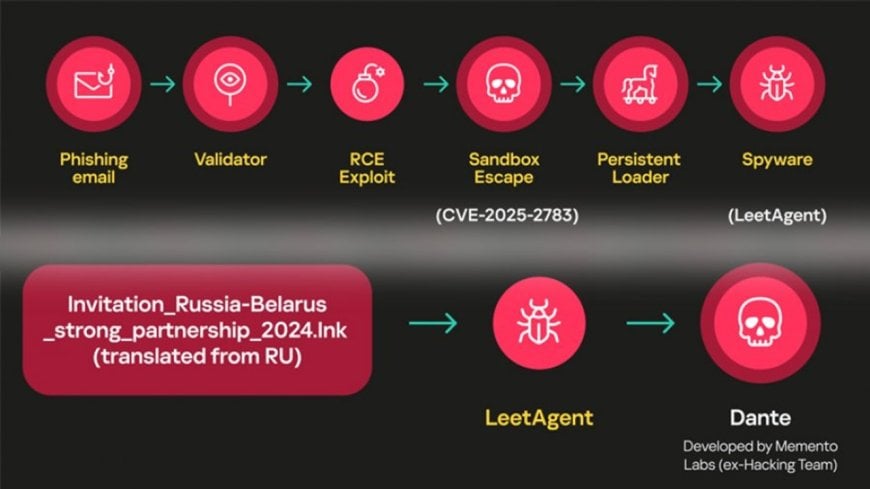
In March 2025, Kaspersky’s GReAT identified a hacking operation titled “Operation ForumTroll.” The attackers exploited a major Chrome browser flaw — Zero-Day CVE-2025-2783 — to target computers across various Russian offices and institutions through phishing emails.
The hackers deployed a spyware tool known as “LiteAgent,” which has been linked to Memento Labs’ more sophisticated spyware “Dante.” Both spyware programs reportedly share similar code structures and technological frameworks.
Kaspersky’s Principal Security Researcher Boris Larin stated, “Everyone knows about spyware vendors, but their programs — especially those used in real attacks — are often very difficult to uncover. To trace the origin of the ‘Dante’ spyware, we had to sift through layers of complex code and revisit long-forgotten data. It’s software with a rather intricate history — perhaps that’s why it was named ‘Dante,’ because tracing its roots was truly a complicated task.”
The “Dante” spyware is designed to conceal itself from detection. The ForumTroll attacks have been active since 2022, primarily targeting computers in Russia and Belarus. Although the threat actors are fluent in Russian, they are reportedly not of Russian origin.
The first detection of “LiteAgent” was made through Kaspersky’s Next XDR Expert system. Detailed research findings and future updates on the ForumTroll APT and Dante spyware are available on the Kaspersky Threat Intelligence Portal.
Established in 2008, Kaspersky’s Global Research and Analysis Team (GReAT) serves as the core of the company’s intelligence efforts, uncovering APTs, cyber-espionage campaigns, major malware, ransomware, and global underground cybercriminal trends.
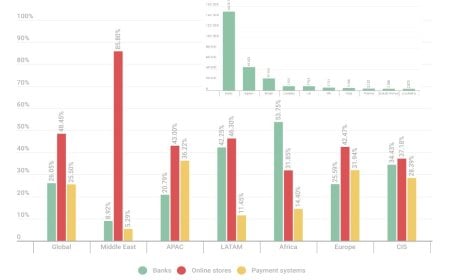
Today, GReAT comprises more than 40 specialists operating across Europe, Russia, Latin America, Asia, and the Middle East. These skilled security professionals lead anti-malware research and innovation through unmatched expertise, passion, and curiosity in cyber threat discovery and analysis.