cPanel Crisis: Critical Authentication Bypass Bug Puts Millions of Domains at Risk

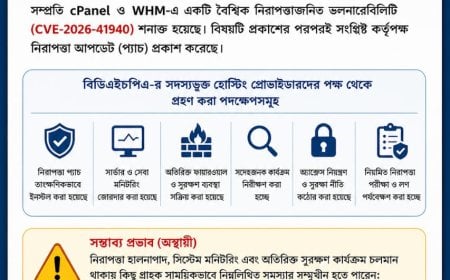
A severe security vulnerability has been identified in widely used web hosting control panels cPanel and WHM, with reports indicating that a large number of websites in the country have already been affected. The issue was confirmed on May 1, just ahead of Zero Day. In response to this risk, cPanel authorities issued an urgent security advisory on Tuesday and released patches or updates for all currently supported versions.
The issue has been resolved in several versions of cPanel and WHM, including 112.0.29, 110.0.97, 108.0.63, and 116.0.5. The company strongly advised that if any server is not capable of updating to a currently supported version, it should be upgraded as soon as possible, as older versions remain vulnerable to this security threat.
Although cPanel has not disclosed detailed technical specifics of the flaw, renowned domain and hosting service provider Namecheap stated that the issue is essentially an “authentication login exploit.” Through this flaw, hackers were able to gain access to control panels without valid user credentials.
As a precautionary measure, Namecheap temporarily enforced firewalls on TCP ports 2083 and 2087, blocking direct access. While this caused temporary inconvenience to customers, access was restored promptly after the patch was applied. According to Namecheap’s support team, the patch was successfully deployed on reseller, Stellar Business, and other servers by the morning of April 29, 2026.
Meanwhile, technology portal TechRadar has warned that the situation poses a serious risk to a significant portion of the internet. Reports indicate that more than 70 million domains worldwide are managed through cPanel and WHM, nearly all of which are now potentially at risk. Since WHM serves as the administrative hub of servers, gaining access to it effectively hands over control of all websites, databases, and user accounts on that server to attackers.
Earlier, researchers from watchTowr Labs uncovered the vulnerability, identified as “CVE-2026-41940,” an authentication bypass flaw. They revealed that attackers could gain full administrative or “root” access to servers without requiring any password. As the vulnerability exists across all currently supported versions of cPanel and WHM and carries a severity rating of 9.8 out of 10, it has triggered widespread concern among server administrators globally.
The cyberattack exploits a technique known as CRLF (Carriage Return Line Feed) injection. By leveraging this method, hackers inject malicious code into cPanel logbooks, effectively disabling session encryption mechanisms. This allows attackers to establish themselves as legitimate root administrators and gain access to sensitive data across all websites, databases, and user accounts via the WHM panel. Hosting provider KnownHost has already confirmed that hackers are actively exploiting this flaw as a zero-day vulnerability to attack web servers.
Typically, restricting access to cPanel and WHM ports (2082–2087) via firewalls is considered sufficient for security. However, in this case, such measures are ineffective. Researchers noted that attackers are bypassing direct port access by using proxy subdomains (e.g., /___proxy_subdomain_whm/login) to enter control panels through standard domains. Additionally, cPanel’s built-in security system “cphulkd” often fails to detect these attacks, further amplifying the risk.
In response, cPanel authorities have promptly released a patch and urged all users to apply it immediately. Technology experts have warned that since attackers can potentially delete all server data or spread malware using this vulnerability, even minor delays in updating could lead to irreparable damage. Cybersecurity analysts have advised system administrators to regularly monitor log files and use high-precision scanning tools to ensure server security.
DBTech/IH/MUIM/OR